
The State of Cybersecurity in Australia
Australian companies are being subjected to at least one cyberattack every 7 minutes. Here's what's happening in Australia and how Packetlabs can provide support.
March 25, 2026 - Blog
Authored By Packetlabs

Passwords continue to be an issue for organizations as users use weak or breached passwords. Just recently, the Canada Revenue Agency (CRA) had a credential stuffing attack used against it in an attempt to gain access to 5,500 CRA accounts; some of the attempts were successful. As more credentials are disclosed in new breaches, the attacks against passwords will continue to rise as the pool of breached credentials give attackers more attempts to gain unauthorized access to accounts.
The probability of your employee using an identical or weak password for their personal accounts and your corporate ones may be higher than you think. However, there are solutions that can prevent this.
Organizations face escalating risk from weak/reused passwords and credential stuffing driven by breached credential dumps.
This article outlines three complementary defenses: use the Have I Been Pwned Pwned? Passwords API in web apps to block known-breached passwords; deploy SpecOps Password Policy in Active Directory to enforce strong, compliant passwords and custom blacklists; and conduct an Active Directory password audit to uncover weak or noncompliant passwords, including service accounts. The audit extracts and cracks password hashes and analyzes patterns with tools like Pipal. Together, these measures provide layered password controls across web applications and end-user systems.
Other than manually checking each password against a known list (e.g., blocking the top 1000 passwords), there is a free API solution by the creator of Have I Been Pwned? that allows you to limit the passwords accepted within your web application. It checks the inputted password against half a billion passwords that were previously breached in a unique and secure way, as described below.
Other than manually checking each password against a known list (e.g., blocking the top 1000 passwords), there is a free API solution by the creator of haveibeenpwned that allows you to limit the passwords accepted within your web application. It checks the inputted password against half a billion passwords that were previously breached in a unique and secure way, as described below.

Once the password check is completed, you can either educate your user but allow the password change, or force the user to select a stronger password that has not been breached.
To prevent users from using weak or breached passwords during a reset or account creation, SpecOps Software released a password policy tool that plugs into your Active Directory. It includes three controls to ensure passwords are as strong as they can be:
Blocks weak passwords by checking previous breaches. Additionally, allows for the creation of a custom blacklist (e.g., Covid2020!)
Allows for compliance-driven templates to ensure compliance with NIST, SANS or PCI
Blocks common character types at the beginning or end of passwords
An Active Directory Audit will assess all the passwords within your active directory for any deviances in your password policy.
Service accounts that never change their passwords would only be picked up by this type of audit. If the previous solution requires months of planning to deploy, the jump to an audit can be done immediately. We also recommend doing an audit even if the previous solution is deployed to ensure the controls are working as intended.
Completing the audit requires obtaining specific files from the domain controller (e.g., NTDS.dit and SYSTEM files) and using them to obtain hashes. We won't get into the specifics but the general process involves obtaining and cracking hashes to uncover cleartext passwords. The cracking is dependent on the hardware used to crack, but generally, the weak passwords are cracked within seconds (e.g., mutations of password, welcome, spring, summer, fall, winter). Once the passwords are cracked, analysis can be done to provide value to the exercise.
To prevent users from using weak or breached passwords during a reset or account creation, SpecOps Software released a password policy tool that plugs into your Active Directory. It includes three controls to ensure passwords are as strong as they can be:
Blocks weak passwords by checking previous breaches. Additionally, allows for the creation of a custom blacklist (e.g., Covid2020!)
Allows for compliance driven templates to ensure compliance with NIST, SANS or PCI
Blocks common character types at the beginning or end of passwords
An Active Directory Audit will assess all the passwords within your active directory for any deviances in your password policy. Service accounts that never change their passwords would only be picked up by this type of audit. If the previous solution requires months of planning to deploy, the jump to an audit can be done immediately. We also recommend doing an audit even if the previous solution is deployed to ensure the controls are working as intended.
Completing the audit requires obtaining specific files from the domain controller (e.g., NTDS.dit and SYSTEM files) and using them to obtain hashes. We won’t get into the specifics but the general process involves obtaining and cracking hashes to uncover cleartext passwords. The cracking is dependent on the hardware used to crack, but generally, the weak passwords are cracked within seconds (e.g., mutations of password, welcome, spring, summer, fall, winter).
Once the passwords are cracked, analysis can be done to provide value to the exercise.
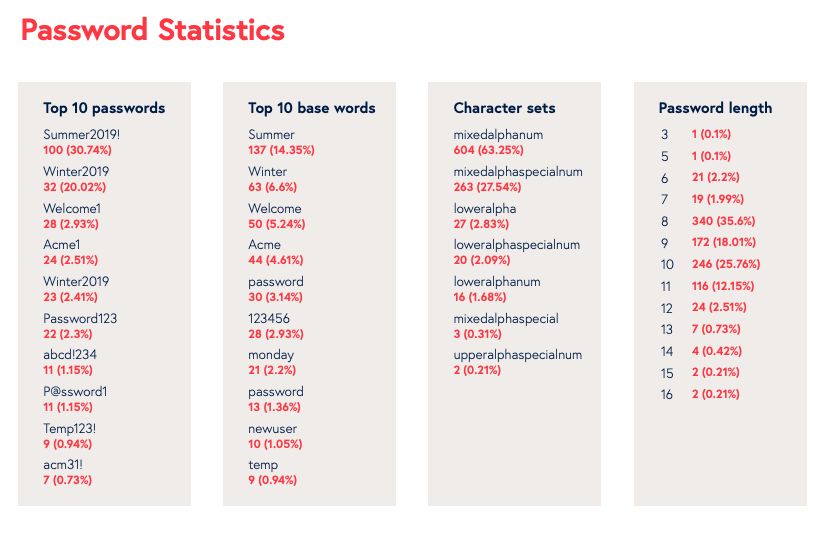
The top 10 passwords are common among the audits we conduct and always come as a surprise to the clients when they receive the findings. The passwords are compliant with their password policy (e.g., length, capital letter, number, special character) but yet are easy to guess.
The need for all three of these solutions will ensure proper password controls are deployed across your web applications and end-user systems.
Question: What is credential stuffing, and why is it getting worse?
Short answer: Credential stuffing is when attackers use lists of usernames and passwords leaked in other breaches to try logging into different services, betting that people reuse credentials. It’s getting worse because more credentials are exposed in new breaches, expanding the pool attackers can test. The recent attack against 5,500 Canada Revenue Agency accounts illustrates how reused or weak passwords make these attempts effective.
Question: How does the Have I Been Pwned (HIBP) Pwned Passwords API help protect our web applications?
Short answer: The HIBP Pwned Passwords API lets your app check user-chosen passwords against a massive corpus—about half a billion previously breached passwords—using a privacy‑preserving method. If a password is found, you can either warn the user but still allow it, or require them to pick a stronger, non‑breached password. This prevents known‑compromised passwords from being set during registration or resets.
Question: What extra controls does SpecOps Password Policy add to Active Directory?
Short answer: SpecOps enhances AD by:
Blocking weak or previously breached passwords and allowing custom blacklists (for example, “Covid2020!”).
Enforcing compliance templates aligned with standards like NIST, SANS, or PCI.
Preventing common character patterns at the beginning or end of passwords. These controls help ensure users can’t set passwords that are formally “compliant” yet still easy to guess.
Question: What is an Active Directory password audit, and why do one even if we enforce policies?
Short answer: An AD password audit evaluates all domain passwords—including often‑overlooked service accounts—for policy deviations and real‑world weakness. It involves safely obtaining domain files (such as NTDS.dit and SYSTEM), extracting password hashes, and attempting to crack them. Weak passwords typically fall in seconds, and analysis with tools like Pipal reveals patterns and hotspots. Even if you deploy policy controls, an audit validates that they’re working and quickly exposes risky accounts that policies might miss.
Question: Why are many “policy‑compliant” passwords still unsafe, and how fast can weak ones be cracked?
Short answer: Compliance (length, uppercase, number, special character) doesn’t guarantee strength if users rely on predictable patterns. Common choices—mutations of “password,” “welcome,” or seasonal words like “spring/summer/fall/winter”—meet rules but are easy to guess and crack, often within seconds. Audits frequently find these in the top 10 passwords, underscoring the need for breached‑password blocking, robust AD policies, and periodic audits together.
Speak with an Account Executive