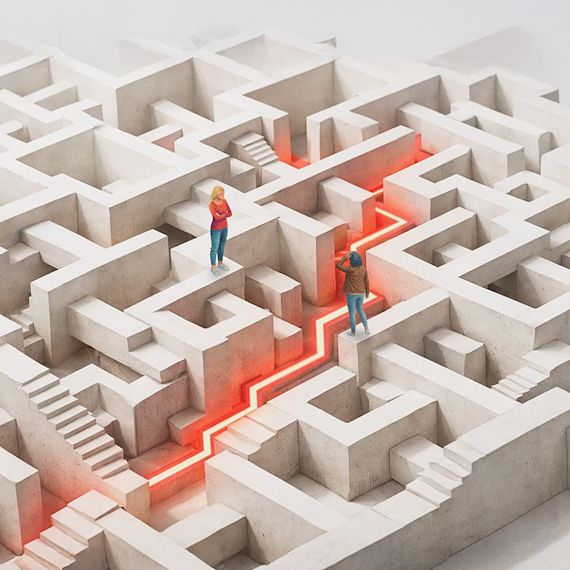
Red Teaming is not a vulnerability scan. It's a controlled, objective-driven simulation that mirrors how real attackers operate gaining initial access, escalating privileges, moving laterally, and targeting crown-jewel assets. We measure not just what's exploitable, but how your organization detects and responds.

Over 42,000 CRA Accounts Breached: What to Know
More than 42,000 Canadian taxpayer accounts have been breached since 2020. Learn more about the data breach class-action lawsuit involving CRA accounts.
May 20, 2026 - Blog