
Why Multi-Factor Authentication is Not Enough
Knowing is half the battle, and the use and abuse of common frameworks shed insight into what defenders need to do to build defense in depth.
September 13, 2024 - Blog

"Is it worth it to report a cyber breach?"
Cybercrime reporting is how law enforcement, national cyber agencies, and industry partners connect patterns, disrupt campaigns, and issue faster warnings. The key is knowing where to report based on country and incident type.
If there’s immediate danger or risk of harm, call emergency services in your area
If money or accounts are involved, contact your bank or payment provider immediately
Preserve evidence: don’t wipe machines or delete emails; instead, collect screenshots, headers, logs, timestamps, and transaction IDs
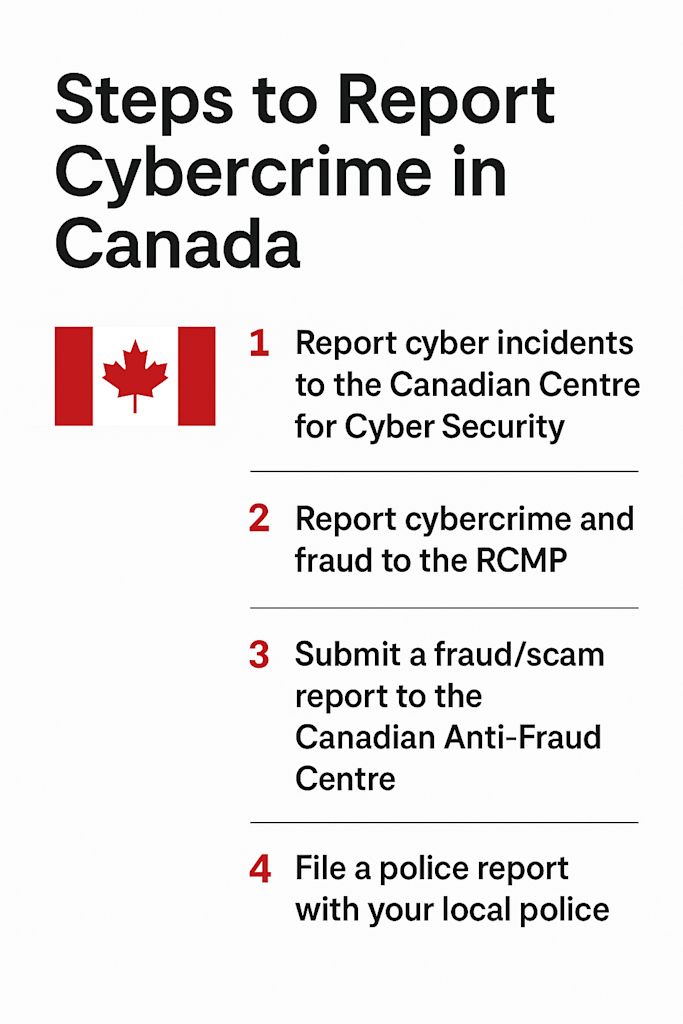
Report using the correct national channel
For guidance on reporting cyber incidents: The Canadian Centre for Cyber Security
For reporting cybercrime and fraud: The RCMP and Canadian Anti-Fraud Centre reporting portal
For reporting fraud and scams: The Canadian Anti-Fraud Centre reporting options
Please note that, while the Canadian Centre for Cyber Security provides support, filing a report through its portal doesn’t automatically trigger a law enforcement investigation. Instead, use the listed bottommost options when filing a report.
For reporting Internet-enabled crimes: The FBI’s Internet Crime Complaint Center (IC3)
For federal reporting guidance and pathways for ransomware incidents: CISA
For general federal direction on cybercrime reporting: DOJ guidance
Note: IC3 is a central collection hub for cyber-enabled crime reports. It's advised to use it even if you’ve also reported locally.

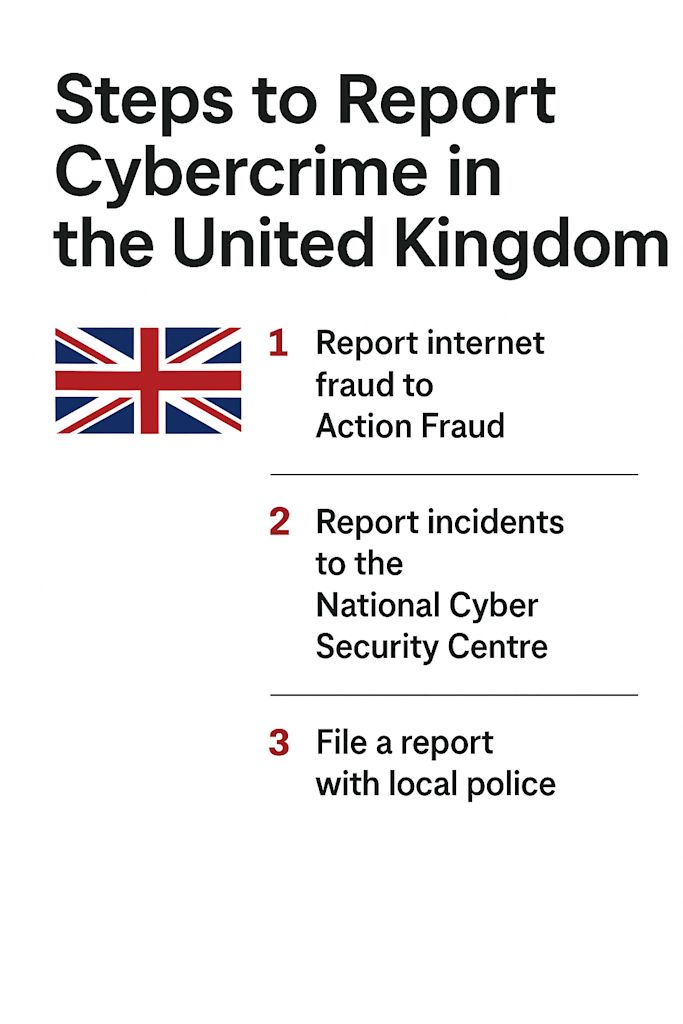
For cybercrime affecting individuals and organizations: The Action Fraud National Reporting Centre
For directly reporting phishing: Forward suspicious emails to report@phishing.gov.uk; report scam texts via 7726
For cybercrime affecting organizations: Report incidents to the UK National Cyber Security Centre (NCSC) via its incident reporting channel
Although all Action Fraud reports are forwarded to the National Fraud Intelligence Bureau (NFIB) for assessment, please note that reporting doesn’t guarantee investigation. However, all reports help to build intelligence and case linkage.
For general cybercrime reporting: Report via the official national portal "ReportCyber"
For cybercrime involving immediate harm or threat to life: Call 000 to report to ScamWatch (per the national guidance)
ReportCyber is run by the Australian Cyber Security Centre (ACSC) and is designed to route reports appropriately.

For general cyber incidents: Report via the national portal
For online scams, fraud, and harassment: Report via the New Zealand Police online reporting pathway (Fraud/Scam/Cyber)
For scam help and guidance: Visit the Netsafe Scams Helpline
Please note that New Zealand government agencies are required to report incidents to NCSC (GCSB) and are encouraged to also report to CERT NZ.

The Timeline: Time of discovery; first suspicious activity; last known-good state
The "who/what": Impacted users, devices, systems, cloud tenants, and domains
The "how": Suspected entry point (phishing, exposed RDP/VPN, OAuth consent, misconfig, or stolen creds)
The indicators: Sender addresses, domains/URLs, IPs, filenames/hashes, ransom note text, wallet addresses
The impact: Data accessed/exfiltrated, encryption, downtime, financial loss, third parties involved
The evidence: Email headers, screenshots, logs (CloudTrail/Azure logs/GCP audit logs), EDR telemetry, or transaction IDs
Is it worth it to report a cyber breach?
Yes. Every time.
Each report helps law enforcement:
Make links between similar reports of cybercrime and fraud across Canada and internationally
Identify and prioritize reported threats and incidents for law enforcement purposes
Coordinate investigations and other law enforcement activities across jurisdictions
Speak with an Account Executive