
6 Ways To Make Your Website More Secure
Here are 6 ways to make your website more secure (and a deep-dive into exactly why it's so vital in 2023 and beyond), all courtesy of our professional ethical hackers.
April 06, 2026 - Blog
Authored By Packetlabs

Penetration testing is an essential part of any cybersecurity strategy or plan. Whether you have an established web/mobile application, network, or other IT infrastructure, it is important to ensure that your security protocols are up-to-date and effective. That’s where penetration testing comes in.
Many companies offer penetration testing services - however, not all are equal. Some companies use automated scanners to look for vulnerabilities or breaches, and some are performed or analyzed by unqualified or outsourced personnel.
How do you find a company that offers more manual testing, a robust methodology and qualified internal staff?
The first step is to understand the methodology used. OWASP Top 10 and SANS CWE 25 are the standards used across each company, but their testing is where the differences are noticed. Many companies utilize automated tools that output a report based on the two standards and provide that report to their clients. While that may sound efficient and potentially cheaper for you, the automated testing alone does not provide end-to-end security coverage and can cost the same as someone who manually tests and has a stronger methodology.
You will need to look for manual testing in addition to automated testing to identify if a methodology is strong or weak. Manual testing will include additional tasks that the automated tool cannot conduct due to the tool’s inability to understand the business logic and flows of the product.
Below is a list of additional tasks that the penetration testing company should have in their methodology:
Can User A view or change User B’s personal information or account settings?
Can user account names be guessed, given a non-standard response is provided when attempting to log in or reset a password?
Is there a lockout mechanism to prevent continuously attempting to guess a user’s password?
Are malicious files allowed to be uploaded?
Can you capture user requests and replay them in the future?
Can you bypass specific verification pieces in a registration flow or change dollar values while attempting to make a purchase?
The list is not limited to the items above, but it will help you begin understanding the maturity of the penetration testing company’s methodology. Once you are comfortable with the methodology provided, you can start reviewing the qualifications of the penetration testers.
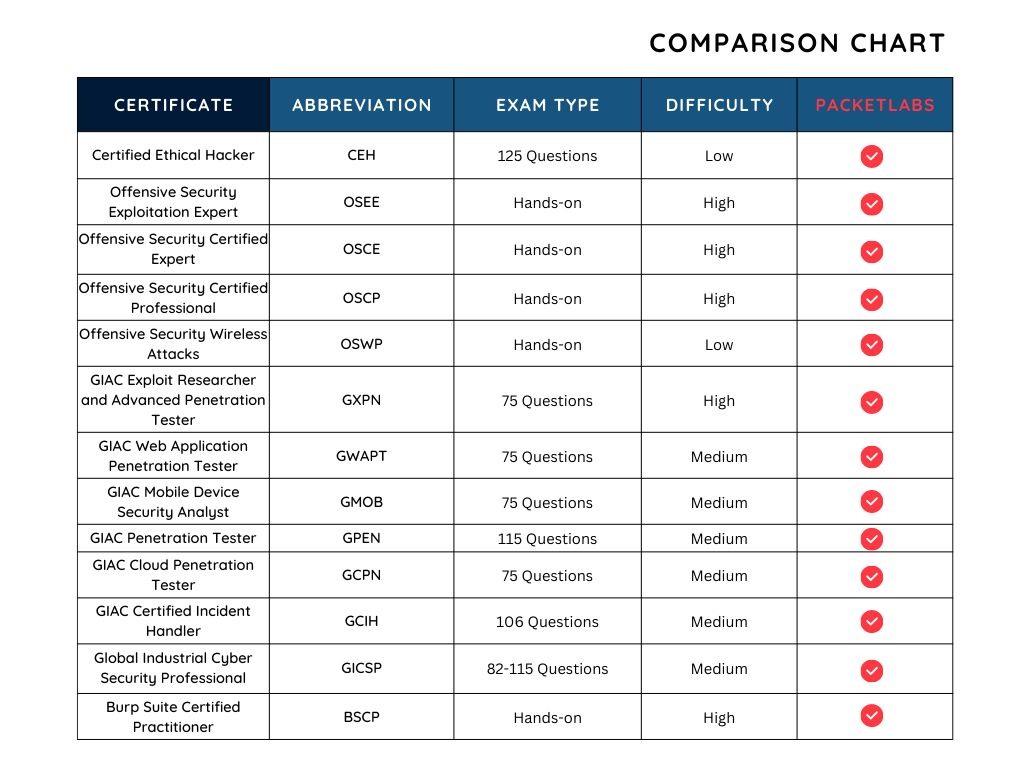
There are many penetration testing certificates, each requiring a different level of difficulty to obtain. One of the more known certificates is called Certified Ethical Hacker (CEH). Unfortunately, the certificate does not provide penetration testers with real-world, hands-on experience and is obtained with little effort through a 125-question, 4-hour exam. Nonetheless, the certificate name sounds qualifying and is accepted by prospecting clients.
As an alternative, we recommend looking for a certificate by the name of the Offensive Security Certified Professional (OSCP) and using it or a similar hands-on certificate as the minimum requirement for your penetration testing company. The OSCP consists of a 24-hour exam where candidates must use practical, hands-on skills to exploit five machines. The exam is used to prove that successful candidates can be presented with an unknown network, enumerate the targets within their scope, and exploit them.
Below is a table of common certificates and the efforts required to achieve them.
It is also important to remember that the certification or qualifications of a penetration tester are only one piece of the puzzle. Keep in mind the methodology, process, reporting and communication with the team when evaluating a company for their services.
What are the organizational certifications held by your company?
Are you SOC 2 Type II accredited?
Who would be conducting a penetration test and what are their qualifications?
Do you perform background and screening checks of your team members?
Do you use contractors for pentesting?
Are all pentesters located in Canada/US?
Which certifications do your specialists hold?
What is your penetration testing methodology?
How do you maintain internal security in your company?
Does your penetration testing service include remediation service?
How much of your delivery is automated versus manual?
How much of the penetration test is tools-based?
Will my services remain available during a penetration test?
Are retests of identified vulnerabilities included?
What methods or channels of communication are used with testers?
Will I have a dedicated project manager?
What is covered in your penetration testing report?
What format are the results available in?
Do you have an example assessment reports available?
Does the ability to retest expire after a specific amount of time?
Did you know that Packetlabs penetration testing services are 95% manual and only 5% automated? This is a testament to our commitment to quality and security. We strive to ensure that the best test results are delivered to our clients. Our manual testing ensures that no stone is left unturned, and even the most subtle of weaknesses can be found and eliminated.
Our team comprises highly experienced professionals with some of the industry’s most sought-after certifications, such as the OSCP, CEH and CISSP. This is just a small example of our commitment to quality and security.
We understand the importance of security, and we always strive to provide reliable results that meet the needs of our clients.
Speak with an Account Executive